Hi everyone, my name is Anugrah SR, I am a Cyber security Consultant and this is my story.
I get a lot of DMs asking, how I got into cybersecurity after graduating masters in biology? I wonder the same, how I transitioned from a scientific research background to cybersecurity. When I look back, I see a long path which I once believed was impossible. I don't know if it's fate, stars aligned, everything happened. As of today, I mark the 100th day of my first job in cybersecurity. Let me try to explain my journey.
Being a hacker is one dream many had. Hollywood movies inspired black hoodies and a terminal with fancy green letters. Huhh...we've all been there. I also dreamt of being a hacker, typing randomly on the keyboard and saying I'm in! During my school days in the computer lab finding the IP address of the computer used by the teacher and messing around using RDP was my first hack!
After a couple of years, one of my close friends Abhishek told me a story about a kid who hacked terrorist emails, helped to secure the nation. We gathered some of his books, which, of course, didn't make any sense back then. We tried to learn ethical hacking but all the efforts were in vain. After finishing schooling in 2015, I got into the Indian Institute of Science Education and Research (IISER) Bhopal. The next 5 years of my life were spent amongst the brightest minds of the nation. New place, new people, new home.
I opted to pursue my master's in life science because it was interesting to learn and there was a lot to explore. I tried my hands on lab work, cell culturing and experimentation, but computational biology caught my attention. I was more interested in learning how a simple combination of an ATGC codon and environment make a blueprint for what we are. I spent most of my days in computer labs and workstations to decode the secrets in genomic sequence, during which I learnt bash scripting and a bit of python that came handy later.
At one time, social media was brimming with news on hackers defacing government websites. I was curious to know how anyone did this, and hence messaged a couple of people in the field, but unfortunately, nobody replied. There were not many resources to learn back then. After wandering around I found it was majorly done by a vulnerability called SQL injection, which starts by including an ' in the URL and a couple of words. BOOM! You have successfully hacked your target website. Then the next popular one was something called XSS, you put a magic word <script>alert("hacked by XYZ")</script> in the target website, you get a popup! Cool, right? Going through a couple of hacker profiles I saw they were getting Sony t-shirts and Intel's appreciation letters. Wow! Do companies give goodies for hacking them? Another strange yet interesting thing for me. But the weird part is, we only hear about people getting arrested for hacking! Why doesn't anyone share this bright side?
The Inevitable
And then while I was at the peak of ecstasy, coding and decoding, slowly but steadily pushing my limits and improvising, to build a career in this passion of mine, I was struck by it. Yes! Behold, the Covid-19 pandemic! One fine morning in March, my phone buzzed with an email notification to leave the campus ASAP! A lot of us had our thesis works that needed to be completed, a farewell party to be dressed up for, and the uncertainty of when we will see each other again. That was the last time I saw my college and the people who made it home.
During the lock-down period, I started to apply for PhD positions in and out of India. In the meantime I wanted to contribute something to the ongoing fight against covid, which made me join OpenVirus as an intern. Here I aggregated scholarly publications and extracted knowledge on viruses and epidemics under the guidance of Prof. Peter Murray Rust and Dr.Gitanjali Yadav from the Cambridge University. I then got interested in looking at my long left Twitter account, where I saw a couple of people doing a challenge on hacking using the hashtag #100daystolearnandimprove.
Compared to earlier years, the number of resources from where you could learn hacking in 2020 was unimaginable. There were so many blogs, free labs, YouTube channels, ctfs, and basically unlimited material available. After the Herculean task of submitting my master's thesis, I wanted to do something new, the only thing that came to my mind was to learn to hack, bug bounties to be precise. Bug bounties is a term used to describe the rewards that companies provide for finding security vulnerabilities in their websites. I started reading blogs, and looking at others' findings. I found out that the issue of missing spf records was an easy bug to find and that people were getting rewarded well with it. So, obviously, I gave it a shot!
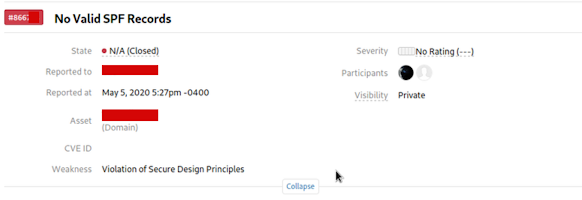
That was the first and last SPF issue I reported! What did it cost? I got negative points on H1.
On May 25th I decided to do #100daystolearnandimprove challenge, because I felt that's the only way I will learn more and be persistent.
#day1 #100daystolearnandimprove
— AnugrahSR | #HackLearnDaily (@cyph3r_asr) May 25, 2020
-> done some bash
-> read some write-up
-> tried to hack on public program found some critical files. Gona report tomorrow
Now looking back, I feel proud of my amazing learning curve. I learnt about owasp top10, the amazing world of recon and more. Click here to see my 100days challenge in twitter
After 3 months of numerous N/A and duplicate bugs, I finally got my first bounty of 100$ for reporting an application level dos attack, I was so happy that day. Adding on, I then got into the top 1000 globally, in bugcrowd. I was building up so much confidence during those 100 days. Unsure if it's the bounties or the dopamine rush from finding a bug, I had second thoughts on my career trajectory. I now started thinking of completely moving into cyber security, rather than having been a scientist first and then moving into pentesting. Indeed, that would have made a good story!
Key Takeaway Points
- Learn to google
- Learn to ask the right question.
- Don't expect someone will spoon feed you, no one gives a F. You have to do your work.
- Engage with the community, gather people around you having the same mindset.
- Network as much as you can.
- Give back to the community.
- Persistence is the key.
- There is no overnight success.
You won't find a bug in 5min or 1hr of testing as you see in these tweet. You just started your journey, it will take hour's, days, weeks or months to find your bug. The people who find fast are the people who knows where to look for them with their experience. Enjoy the process!
— AnugrahSR | #HackLearnDaily (@cyph3r_asr) October 15, 2020
Infosec twitter is a great place where apart from the occasional drama, you will learn a lot, and can directly talk to experts in the field but the best part is the GIVEAWAYS! My life turned when I received a 3 months Tryhackme subscription from John Jackson and Pentesterlab sub from Sillydaddy. I spent days and nights solving labs, and learnt as much as I could.
If you are a beginner, I would highly suggest Tryhackme, they teach you from the basics. Once the basics are cleared you can move on to other resources. More details on how to get started will be covered in an upcoming blog!
Infosec internship.
One day I saw a tweet from RogueSMG that Securelayer7 was hiring based on a ctf challenge. A ctf challenge is where you will be given vulnerable machines, and you need to hack it to get a flag. I was having this self doubt about who is going to hire me with a non technical background and zero relevant certifications. All the job advertisements I saw had CEH, OSCP, engineering degrees and 2-3 years experience as requirements. So I took these ctf challenges as my proving ground. I was able to solve most of the challenges, send a nice report, and within a week, after two rounds of interviews I was offered an internship position, which I gladly took. I will be forever grateful to Sandeep Kamble and Securelayer7 for taking a chance on me. During my internship at SL7, my task consisted of application testing, client meetings, report writing and more. These experiences at Securelayer7 made me clear that this is what I want to do! This is my career path.
First job
After couple of months later I got an unexpected message from Vishnu, asking if I'm interested in full time job in UST, he gave me a reference, after interview and technical round, I got my offer letter! My first job as Cyber security analyst. Working with most talented people in the field, updating and upgrading my skill sets and protecting the organization from potential threats, its pretty cool if ask me. Cherry on the top I became a Synack red team member on June. I would wish to thank everyone who played a pivotal role in my life, this wouldn't be possible without the help of this amazing community and inner circle of mine. Did I took the right decision?
So that's how I ditched my lab coat to wear the white-hat!
If you want to know more about me, collaborate with me or you need help in anyways, contact me on twitter or LinkedIn
Some Additional Info
I delivered a talk on my infosec journey during Infosec Writeup's first-ever virtual conference.
This blog was originally published at P1Boom
Are you also trying to get into cybersecurity? Do you also have a non-tech background? I can be your unfair advantage!
Join in a call with me, if you are looking for a mentor, help with interview preparation, resume review, to get started and more 👇


